Setup CrowdStrike's Device Controle
The Device Control module allows you to control the use of USB devices (USB keys, hard drives, etc.). Concretely, Device Control allows you to create a USB device Policy: you define general rules that allow or block USB devices based on their class.
What is possible:
Configuration by device type
Implemented using CrowdStrike Policies, either by you or by the Stoïk SOC
Configuration of exclusions (workstation, device)
Can be managed with the “Device Manager” user right
What is not possible:
Configuration by endpoint
This would require assigning each endpoint to specific groups
For example, you can create a policy to block USB storage devices while allowing access to other USB device classes.
Deployment by the Stoïk team
Self-service deployment
Policy deployment
1. Deployment by the Stoïk team
1.a. Define your control objectives
Determine what you want to enforce:
❌ Block all USB devices
👁️ Set devices to read-only
✅ Allow only specific models
📊 Monitor / audit usage without blocking (observation mode)
1.b. Inventory of authorized or blocked devices
For each USB key or device you want to allow or block:
Plug it into a workstation
Retrieve its hardware identifiers (Windows procedure below)
Manually, via the graphical interface:
Device Manager > USB device
Right-click > Properties > Details > Hardware IDs
Automatically, via the PowerShell console:
Send the information to the Stoïk team at [email protected]:
Vendor ID (VID)
Product ID (PID)
Serial number (if applicable)
1.c. Deployment by the Stoïk team
A Stoïk cybersecurity engineer configures the rules and informs you once the setup is complete.
2. Self-service deployment
For self-service deployment, request “Device Control Manager” access to your CrowdStrike console by emailing [email protected].
Click Create policy
Enter a name and a description (optional) for your policy
Click Create policy to validate
In the Settings tab:
Select the mode to use: Monitor, Monitor and enforce, Off (macOS only)
Enable the desired USB settings to include USB devices in the policy
Select the notification to inform end users when a USB device is fully blocked
Select the notification to inform end users when a USB device is restricted
The modes mentioned above correspond to different configurations of the Device Control option. There are three distinct modes
Monitor and enforce: Actively applies defined rules — blocks or allows USB connections and logs activity. Allows you to track connection attempts and block unauthorized ones.
Monitor only: Logs connections and actions without enforcing restrictions. Ideal for initially testing policies without disrupting users.
Off (macOS only): Completely disables Device Control protection; no activity is logged or blocked.
⇒ Using a policy in Monitor only mode is an effective way to accurately establish a list of USB devices typically used by your employees. This list can then serve as the basis for a future allowlist of authorized devices.
Go to the USB Device tab
To select the USB device classes to include in the policy, open the USB Device tab
Click to expand each device class to include
Choose the authorization level for each device class
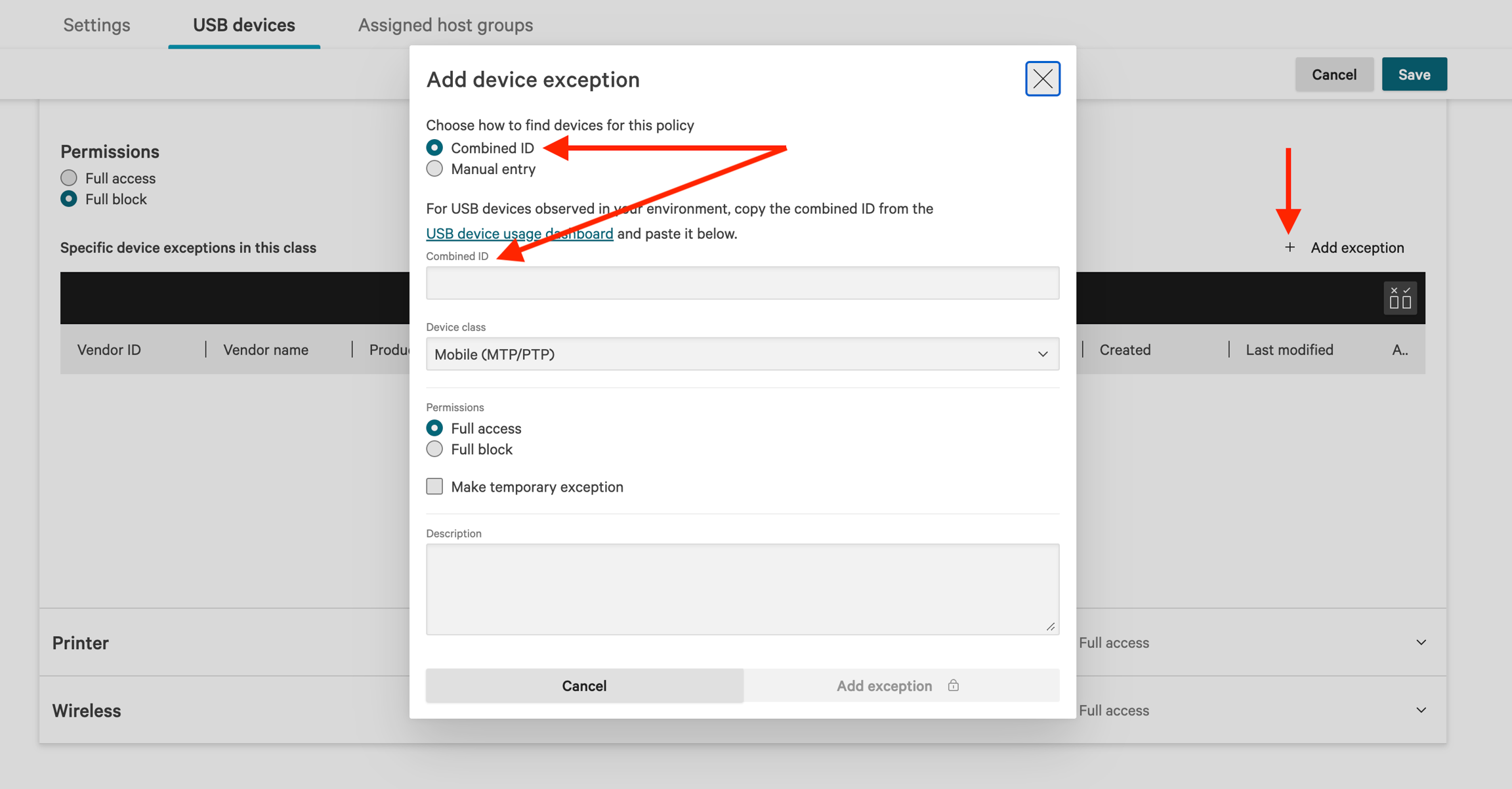
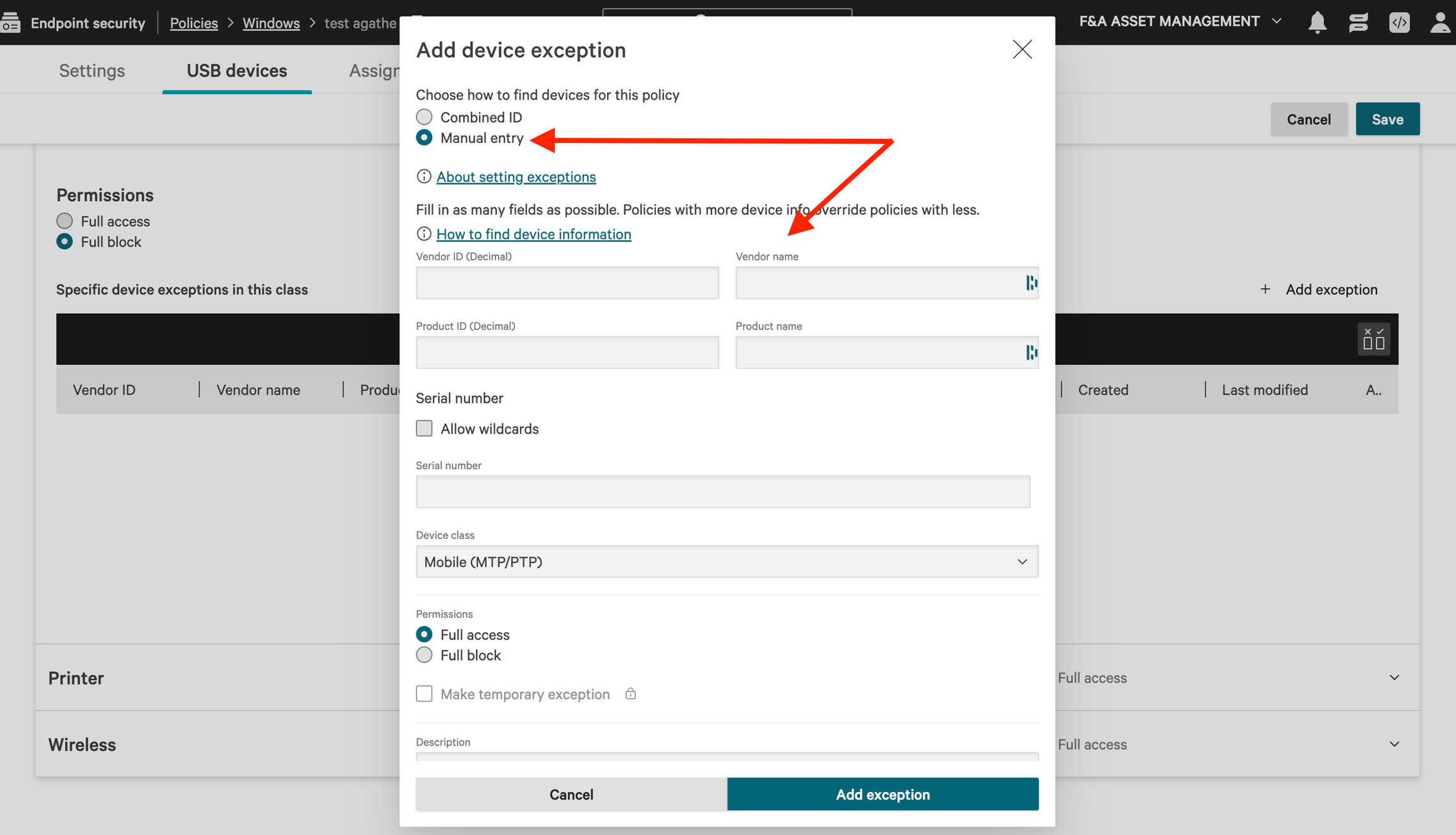
Add exceptions per class if needed by clicking Add exception. Enter the USB port either using its combined ID or via manual entry
b. Click Save in the top-right corner, then click Save again to confirm.
Go to the Assigned host groups tab
Click Assign host groups to policy
Once configuration is complete, click Enable policy
💡 To speed up the configuration of similar policies, click Duplicate policy to create an exact copy. Then open the copy and adjust the name, settings, authorization levels, and exceptions as needed.
3. Policy deployment
Windows: Device policies are applied as soon as a USB device is connected to a host. If USB devices are already connected to a host at the time the policy is assigned, they will only be affected upon their next reconnection or the next host reboot.
macOS: Device policies are applied as soon as a USB or Bluetooth device is connected to a host. If USB or Bluetooth devices are already connected at the time the policy is assigned, the policy takes effect immediately. In other words, if the policy blocks the device, it will be disconnected.
Last updated
Was this helpful?

